Built-in paths for RCE, C2, and data leaks via code execution, web access, and MCP integrations.
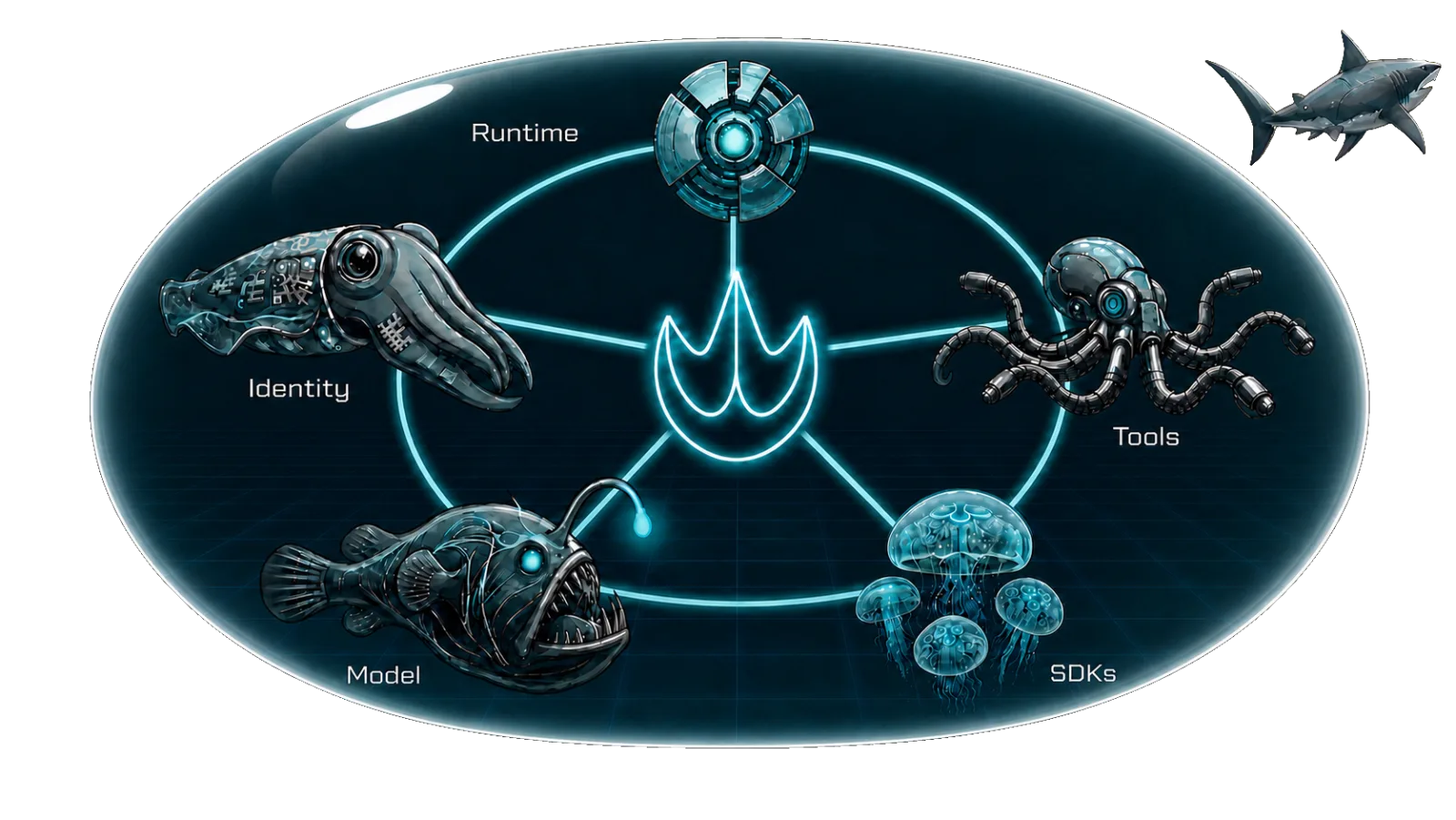
Enterprises are no longer just using AI tools. They are scaling their workforce with hosted AI agents. These agents act like employees: gathering data, executing code, and taking high-privilege actions. Every production agent is built from the same five components, each with its own attack surface.
Built-in paths for RCE, C2, and data leaks via code execution, web access, and MCP integrations.

Managed runtimes include provider components. You're left tracking vulnerabilities you can't touch.

Open-source frameworks ship fit-all defaults. Safe in one setup, catastrophic in another. The mismatch is yours.

Guardrails are probabilistic. They live at the model layer and miss attacks that bypass the model.

Components, tools, and data tied by one policy. One compromised tool means a full agent compromise.
Continuous discovery and risk-scoring of every agent the organization runs - sanctioned, unsanctioned, and shadow. Each agent is mapped to the permissions, tools, secrets, and data it can reach, so the blast radius is known before compromise.
Real-time, intent-aware authorization of every agent action - at the tool-call layer, not just the prompt layer. Catches the attacks model guardrails miss, including direct tool exploitation, lateral movement between agent components, and unintended execution paths.
Every agent, every tool invocation, and every cross-agent call is a distinct request that must prove who it acts for, why, and in which context - before it gets access.
Support bots, customer success agents, and sales assistants interact with users you don't control while accessing internal systems. Agent goal hijack and memory and context poisoning are invisible to existing security tools. Grit enforces a hard boundary between what the agent reads and what it can act on.
Agents built for internal operations are permissioned to create records, grant access, and trigger workflows on behalf of users. Tool misuse and exploitation and identity and privilege abuse can turn a single request into irreversible damage across systems. Grit binds permissions to the declared scope of each request before actions execute.
Healthcare providers, financial institutions, and insurers deploy agents across their most sensitive data. The regulatory bar doesn't lower because the worker is an AI. Rogue agent behavior causes data leakage. Human-agent trust exploitation turns automation bias into liability. Grit provides the audit trail proving every data access was authorized.
In most organizations, agents reach production before security is involved. Without inventory, blast radius is unknown and agentic supply chain vulnerabilities are invisible. Grit discovers and risk-scores every agent, mapping each to the permissions, tools, and data it can reach, enforcing a consistent security posture across every cloud and platform.
A HAAP2 (Hosted AI Agent Protection Platform) is a security platform that discovers every AI agent across an organization, governs every action they take, and defends every layer of agentic infrastructure on any cloud or platform. The category was coined by Grit Security.
Guardrails operate at the model layer and rely on probabilistic filtering of prompts and responses. A HAAP2 operates at the tool-call layer and enforces deterministic authorization on every agent action - including ones that bypass the model entirely, like direct tool exploitation and lateral movement between agent components.
Grit's runtime layer inspects every agent tool invocation in real time and authorizes it against the agent's declared scope before execution. It catches attacks that model-level filters can't see: direct tool exploitation, cross-component lateral movement, and unintended execution paths.
Grit is vendor-neutral and works across any cloud, any managed agent platform, citizen-developer tools, custom frameworks, and SaaS-embedded copilots. Coverage is unified - one platform inventories every agent and enforces a consistent posture without swiveling between consoles.
Tools, Runtime, SDKs, Model, and Identity. Each has its own attack surface, and Grit defends all five from a single platform: tools that enable RCE and data leaks, managed runtimes you can't patch, SDK fit-all defaults, probabilistic model guardrails, and identity boundaries that collapse on a single compromise.
Security teams at enterprises running production AI agents - customer-facing assistants, internal automation, and agents operating on regulated data and PII. It's also for security teams getting visibility into shadow AI that engineering shipped before security was looped in.
See how Grit gives your security team a single platform to discover, govern, and protect every hosted AI agent.